How to Configure your Network Tab
The Network tab controls what your ABS will do for your Network.
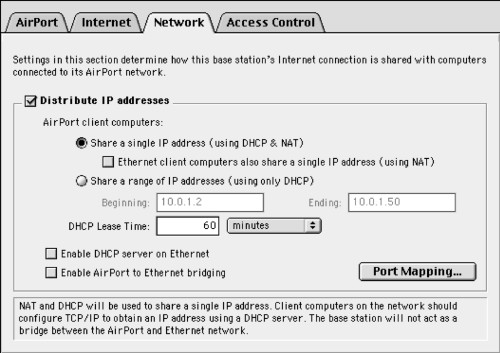
Your ABS is a very versatile piece of of Networking equipment. Many different configurations are possible, all dependant on how you want to use the ABS. For example, the Airport software allows the ABS to act as a router and as a rudimentary firewall. It does this through a process called Network Address Translation (NAT, also known as IP spoofing). This software is activated when you check the "Distribute IP Addresses" box.
Below, I have tried to assemble the most obvious combinations, one of which hopefully comes close to describing what you want to do with it. Red Line connections denote ethernet wires, blue connections denote telephone wires. If any option is grayed out (for example, due to you unchecking the "Distribute IP Addresses" option, you can assume that these options are automatically disabled.
Telephone Dialup Connection
 |
This is the configuration you would use if you have a regular dialup connection to your ISP. As the ABS has a WAN/LAN port built-in, you can share this connection across wired and wireless computers alike. If you want to attach multiple computers via wired connections, you'll need to attach a ethernet "hub" or "switch" to the ABS, then attach the computers to the hub/switch. In this configuration, I would:
This way, your ABS allows the wired and wireless computers to talk to each other (useful for printers, for example), hide all computers behind the ABS Firewall (a good safety feature), and maintain ease of setup because the ABS distributes IP addresses to all the computers on the network, wireless or not. Note: The Graphite ABS firmware does not allow VPN connections to work whenever the NAT Firewall is enabled. To the best of my knowledge, there is no foolproof workaround, besides upgrading to a later base station or using a router (see below). |
|---|
Office Network
 |
In an office that already has a IT infrastructure, the ABS usually functions as a mere "bridge" between the wired and the wireless portion of the network. Thus, it does not need to be a router (offices usually have one already) or a DHCP server. It is very important not to have multiple DHCP servers on one network (it causes a lot of confusion, see below), so the following steps are important:
However, the last three options are likely to be grayed out once the "Distribute IP addresses" box has been unchecked. Don't worry, it'll work. Since NAT is turned off in this configuration, VPN connections should work without issues. |
|---|
High Speed Internet
 |
As your ABS only has one LAN/WAN port, a base station that is attached directly to an high-speed modem can then only serve wireless clients. Therefore, it will not be able to bridge between wired and wireless computers. If want to hook up wired and wireless computers, you'll have to use a router (see below). If all you have is wireless clients, this is what I would do:
Virtual Private Connections (VPNs) will not work with a Graphite ABS that has NAT turned on. Thus, if you need to make PPTP, IPSec, etc. connections to reach work, you'll either have to upgrade to a later base station or use a router that does pass VPN packets. |
|---|
High Speed Internet with Router
 |
If you desire to create a network consisting of multiple wired and wireless computers all hooked up to a high-speed modem, you'll need a router that has multiple ethernet ports to accomodate the ABS and the wired computers. Most routers have four ethernet ports on the LAN side, so if you have even more wired computers, printers, etc. to attach, you can add an additional hub or switch. As all routers I know of have a DHCP server and a NAT Firewall built-in, the ABS does not have to fulfill either function and hence:
|
|---|
If one of these scenarios fit your situation, it's time for the Access Control Tab. If not, or if you would like to get a better understanding of what NAT, DHCP, and Port Mapping do, I hope the following discussion is illuminating...
Network Address Translation (NAT) Explained
NAT "hides" machines behind the ABS from prying eyes on the internet. Basically, it pretends to be the only client attached to a internet connection and it prevents any unauthorized access to the network behind the ABS (this protection is what people usually refer to as a firewall). Hence, a firewall is a very important security feature as it prevents infected computers on the internet from contacting your machines, for example.
You might think that your computers are reasonably up-to-date, that they have built-in firewalls, etc. yet the continuing soap opera on the Windows side of the computer business shows otherwise. A recent test showed that the average life expectancy of a unpatched, unprotected windows computer on the internet is four minutes... While Apple Macs are far more resistant to outside attacks, a external firewall remains a worthwhile and important security tool.
Another benefit of a router is that the number of machines behind it remain masked from the ISP. This is beneficial whenever your ISP tries to impose arbitrary limitations, such as the maximum number of clients that may connect at the same time. However, the more machines share a single internet connection, the slower the connection will become for each user as the bandwidth is shared equally. This is particularly apparent on telephone dialup connections.
Enabling NAT on a Graphite base station does slow the network connection down somewhat as the CPU in the Airport base station tries to keep up with the torrent of data moving through it. The faster the network connection, the more the added "overhead" of NAT becomes an issue. For dialup modem users, NAT on a ABS is transparent - the network connection is far too slow for NAT to have an impact on throughput. However, any slowdowns due to NAT is usually insignificant compared to the many other things that slow down internet connections.
A serious downside to the Graphite ABS NAT implementation by Apple and Karlnet was that the NAT built into the "Graphite" ABS did not allow most Virtual-Private-Network (VPN) packages to work (IPSec packages like the Nortel Extranet for example). Click here for an explanation of NAT from Apple
The DHCP Server
Regardless of how many machines are on your network, it is useful to have something called a DHCP server. Think of a DHCP server as something similar to the telephone company assigning telephone numbers to houses in your neighborhood. These numbers (IP addresses) then allow the devices on your network to communicate with each other.
The way that the router keeps track of which device is via something called the MAC address, which is a unique series of hexadecimal digits assigned to every ethernet transceiver when it is built. Thus, every transmission destined for a specific IP address is then picked up by the transceiver that "knows" that this is its IP address.
With a DHCP server, each ethernet transceiver is assigned a valid IP address automatically using the MAC address of every device on the network. In turn, the devices on the network can be programmed to accept such designations automatically. Thus, the DHCP server is a great time saver because it ensures that every piece of your network knows how to reach each other and how to connect to the internet.
With the help of a DHCP server, all computers in your home are automatically assigned an IP address and download critical router, DNS server, subnet, etc. data. If anything changes upstream (like your ISP putting you on a new network node), a DHCP server will automatically reconfigure the TCP/IP settings of your networked machines. Hence, it is not surprising that nearly every network in existence today has a DHCP server - they save a lot of time. Most (if not all) routers sold into the home market today have built-in DHCP servers.
However, there is one thing about DHCP servers that you have to keep in mind: They cannot coexist on a network. DO NOT EVER run two or more DHCP servers on the same network - confusion will reign. It's like two policemen directing traffic in an intersection without coordinating with each other! Whenever two DHCP servers are battling for control, some machines on the network will not be able to connect to the internet, etc. as they may erroneous DHCP data being sent to them.
The DHCP lease time is the amount of time that a individual computer retains its network address. Think of it as a dinner reservation - its a time slot reserved for you. This is particularly relevant for networks where a lot of machines come in and out. The shorter the time slot, the more turnover can be accommodated. However, renewing DHCP leases causes some overhead and if you do not have a lot of people moving in and out of your network, you can safely set long DHCP leases. The default 60 minutes is usually good enough. Click here for a explanation of DHCP from Apple
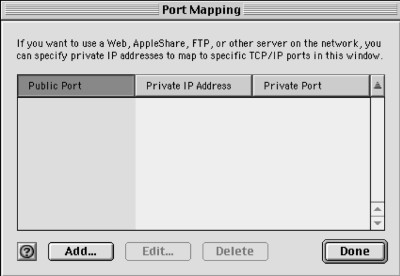
Port Mapping
Port mapping is a way to allow outside connections through your firewall. For instance, if you want to have the ability to connect to your home network via the internet, you can configure port mapping to allow you to reach a specific machine on your network behind the firewall for a specific service.
For example, you may wish to allow Secure-Shell (SSH) connections to a server at home because you like to listen to your iTunes collection at work. Or you may have a web-server that serves up pages via your ISP. Either way, Port-Mapping is most interesting to folks who have high-speed, "always-on" ISP connections.
The first thing you have to do is determine what services you need and what ports they run on. For example, HTTP connections run on port 80, while SSH connections are found on Port 22. For e-mail, SMTP servers typically use port 25 while POP servers are typically found on port 110. You get the idea.
In order to make your life easier, you should assign whatever server you have a static IP address. Otherwise, if your DHCP server decides to re-assign the current IP number to a different machine, you won't be connecting to what you want to. Then tell the ABS what external port addresses correspond with what internal addresses. You do this by clicking on the Add button.
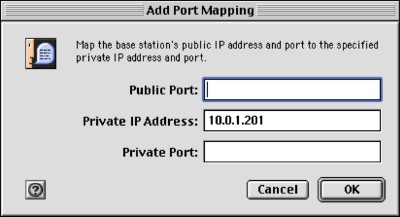
Here then, you tell the ABS how to route external requests inside your network. For instance, if my web server has a private IP address of 10.1.201, then the entries would be 80, 10.0.1.201, and 80. Then, any request for web-pages that the ABS receives will be forwarded to the machine at 10.0.1.201, processed, and replied to.
In order to use these services, you have to know the IP address that your ISP has assigned to you. Unfortunately, most ISPs use dynamically allocated IP addresses for your WAN connection, that is they can change. Typically, users have to pay a premium to receive a static IP address. If you're going to use Port Mapping a lot, then having a static IP address assigned to you will make your life a lot easier. However, there are some services like DynDNS to elegantly get around those limitations.
See, I told you it could be complicated. Anyway, onwards to the Access Control Tab!


